
Windows Universal Tool is from the same family as Windows Utility Tool malware. The Trojan changes Windows registry so that the fake scanner starts before your normal Windows desktop is shown. Just run a fake system scan and then close the program in order to get to your normal Windows desktop.
Fake Windows Universal Tool scan results:

Windows Universal Tool software description:

You will also get this web form where you can purchase a license of Windows Universal Tool. One year subscription + life time support will cost you $80.

If you have paid for Windows Universal Tool then you should contact your card supplier's fraud department and ask for the payment to be cancelled. Just tell them that this software is an infection. As you can see, this program gives a false sense of security and reports non-existent viruses. If you somehow got hit with this scareware, please follow the steps in the removal instructions below. Be advised that Windows Universal Tool may come bundled with other malware. That's why you should scan your computer with anti-malware software even if you managed to remove the rogue program manually. If you have any questions or help removing this virus, please leave a comment. Good luck and be safe online!
Windows Universal Tool removal instructions:
1. Rename the main executable of Windows Universal Tool:
In Windows XP:
C:\Documents and Settings\[UserName]\Application Data\[SET OF RANDOM CHARACTERS].exe
In Windows Vista/7:
C:\Users\[UserName]\AppData\Roaming\[SET OF RANDOM CHARACTERS].exe

Look for htwlfy or similar file and rename it to malware. Then restart your computer. This should disable Windows Universal Tool. After reboot, please continue with the rest of the removal process. NOTE: By default, Application Data folder is hidden. If you can find it, please read Show Hidden Files and Folders in Windows.
OR you can download Process Explorer and end Windows Universal Tool process.

2. Download shell-fix.reg. Double-click to run it. Click "Yes" when it asks if you want to add the information to the registry. This file will fix the Windows Shell entry.
3. Download free anti-malware software from the list below and run a full system scan.
NOTE: in some cases the rogue program may block anti-malware software. Before saving the selected program onto your computer, you may have to rename the installer to iexplore.exe or winlogon.exe With all of these tools, if running Windows 7 or Vista they MUST be run as administrator. Launch the program and follow the prompts. Don't forget to update the installed program before scanning.
4. New threats appear every day. In order to protect your PC from such (new) infections we strongly recommend you to use ESET NOD32 Antivirus.
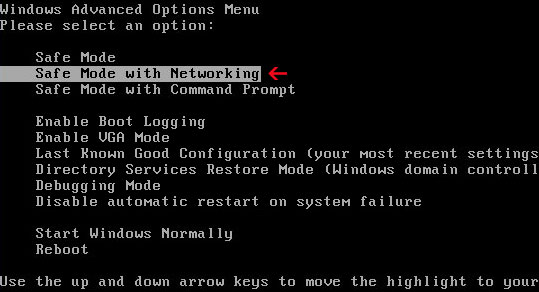
Alternate Windows Universal Tool removal instructions (in Safe Mode with Networking):
1. Reboot your computer is "Safe Mode with Networking". As the computer is booting tap the "F8 key" continuously which should bring up the "Windows Advanced Options Menu" as shown below. Use your arrow keys to move to "Safe Mode with Networking" and press Enter key. Read more detailed instructions here: http://www.computerhope.com/issues/chsafe.htm
NOTE: Login as the same user you were previously logged in with in the normal Windows mode.
2. Download free anti-malware software from the list below and run a full system scan.
NOTE: in some cases the rogue program may block anti-malware software. Before saving the selected program onto your computer, you may have to rename the installer to iexplore.exe or winlogon.exe With all of these tools, if running Windows 7 or Vista they MUST be run as administrator. Launch the program and follow the prompts. Don't forget to update the installed program before scanning.
3. New threats appear every day. In order to protect your PC from such (new) infections we strongly recommend you to use ESET NOD32 Antivirus.
Associated Windows Universal Tool files and registry values:
Files:
In Windows XP:
- C:\Documents and Settings\[UserName]\Application Data\[SET OF RANDOM CHARACTERS].exe
- C:\Users\[UserName]\AppData\Roaming\[SET OF RANDOM CHARACTERS].exe
- HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Winlogon "Shell" = "%UserProfile%\Application Data\[SET OF RANDOM CHARACTERS]"
No comments:
Post a Comment