Table of Contents:
Description of Cyberbullying"Cyberbullying" is when a minor or group of minors are trying to harm another underage person by using various information and communication technologies, such as Internet, mobile phones or other digital and interactive tools. However, this term should not be confused with cyberstalking or cyber-harassment, where the adults are involved.
In fact, when adults are threatening or embarrassing someone else, it is never called cyberbullying. Even if adult is attempting to seduce children and meet them in real world, it is called differently – sexual harassment, sexual exploitation or simple luring by a sexual offender. Nevertheless, in some cases those sexual offenders are also involved in cyberbullying, especially when they get intrigued by sexual harassment among the children, or even worse, when they find advertisements posted by bully and offering a victim for a sex.
The methods of cyberbullying can be extremely different and practically depends only on child’s imagination and access to technology. However it’s obvious, that any kind of these actions must be stopped or at least prevented as soon as noticed. And not only because of negative effects on children psyche and behavior, but also because of real danger concealed in cyberbullying actions, such as killing each other or committing suicide.
To avoid these terrible things happening, you should be aware of any signs of cyberbullying. The fact is that it is usually repetitive communication and when parents see it, they commonly feel concerned about improper language among the kids and do not realize how these rude and embarrassing posts may hurt emotionally or even physically their own or any another child. Moreover, sometimes there is no clear distinction between the good and bad sides, because the kids often change roles: from victim to bully and vice versa, and therefore the cyberbullying must be stopped from both sides.
Most of the time, the cyberbullying does not go that far, but sometimes it can reach the level of misdemeanor or juvenile delinquency charge, while serious criminal cases, such as theft of identity and/or password, have to be considered according to federal or state law. However the most common and at the same time the mildest penalty for children is banning their ISP or IM accounts due a terms of service violation. These criminal charges are often tried and pursued by concerned parents.
Sometimes schools are also trying to control students and their cyberbullying actions, even if they are carried out outside the school area or school hours. Unfortunately, this is usually treated as excessive desire to demonstrate the authority or simple violating the student’s free speech right. Despite of that, schools can still be very effective in preventing and stopping the cyberbulying situations, especially when working together with parents. The first thing they can and should do is to include the cyberethics and law into their education program. They can also try to find a creative way to control off-campus cyberbullying attack without being blamed for exceeding their legal authority. For example, the additional rule can be added to the school policy allowing to discipline and control students who are violent or disrespectful with other students, even if their actions are taken off-campus. In this case the constitutional issue becomes a contractual and the reason to criticize school actions is overridden.
Different Kinds of CyberbullyingMainly there are two types of cyberbullying:
direct attacks and
indirect attacks (cyberbullying by proxy). Generally speaking, either cyberbullying is executed by bullies themselves or they use others to help them in cyberbullying.
Direct AttacksDirect attacks can be divided in eight smaller groups:
- Sending Inappropriate Text Messages;
- Sending Inappropriate Pictures, Videos or Junk;
- Sending Malicious Codes;
- Writing Blog Posts or Creating Web Sites;
- Malicious Online Impersonation;
- Stealing Passwords;
- Internet Polling;
- Interactive Gaming.
1. Sending Inappropriate Text Messages. Instant messaging or harassment by text messages is probably the most popular way of direct cyberbullying attacks. Children may send embarrassing or threatening messages and don’t realize that it is just as harmful as bullying in the real world. Moreover, sometimes messaging grow up to big text wars or serious text attacks, when thousands of text messages are send to victim’s mobile or computer device.
Actually, online messaging has even more variations. For example, many ISP (Internet Service Providers) blocks a user, which is writing or telling inappropriate things according to other users’ claims. However when this tool is used for blaming harmless people (in order to kick them offline for a certain period), it becomes as a game or prank and is called "warning wars". Also, a child or teen may create an account name which is almost the same as another child’s name and try to damage his/her reputation by saying and doing inappropriate things.
2. Sending Inappropriate Pictures, Videos or Junk. Just like messages, various pictures, videos or other junk might be send through e-mail, IM or mobile phones. Sometimes a picture of nude classmate (captured in the shower, locker or dressing room) or any other funny, vulgar or pornographic picture of teen is send to all e-mail or phonebook contacts. This may even cause an uncontrollable chain reaction when pictures are passed around to hundreds of children. Later these pictures may be posted on a website or sharing program for anyone to download. Well, we can only imagine the feelings of the victim after such events.
Sending porn and other junk is carried out in slightly different way. Cyberbullies often use victim’s e-mail address or IM name and registers him/her in various websites, usually in the ones, which are inappropriate for children (e. g. adult site). Then the victim receives hundreds of e-mails with junk or pornographic pictures and has a lot of problems if teachers or parents notice them (the adults might become very concerned about child behavior, assuming that he/she is visiting the porn sites).
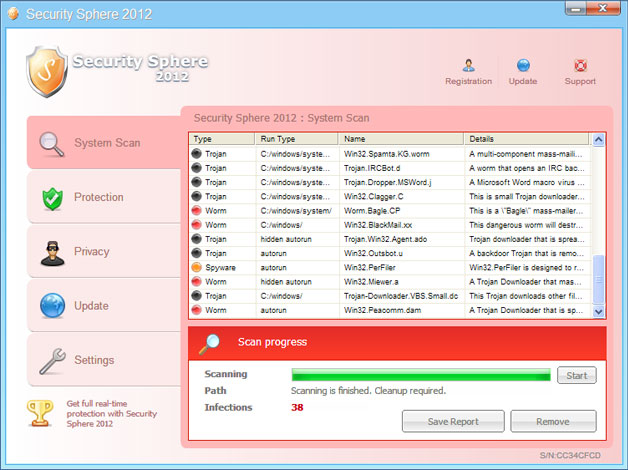
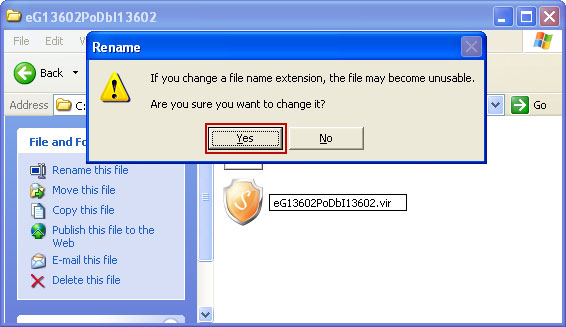
3. Sending Malicious Codes. In order to spy on victim or to damage his/her computer, children can send malicious malware. The code is usually sent as an email attachment, link or simply placed on a website, frequently visited by victim. Opening infected files usually results in lost data (when malware is used to erase the hard drive) or lost of computer control (when bully takes over the computer by operating remote control software).
4. Writing Blog Posts or Creating Web Sites. Nowadays, having your own blog or website has become very easy, so easy, that even a child can create it and, in some cases, use it for harming others. In some cases they just are posing as the victims and blaming innocent child, and in other cases they just put false, distorted or rude posts about the victims and their personal life.
For example, the actual purpose of blogging is to publish personal thoughts, various Web links or any other kind of stuff and share it with other people. However sometimes kids or teens use these blogs to destroy another child’s reputation or to reveal his/her personal information. Considering the vulnerability and sensibility of young people, any false or rude and humiliating posts about their appearance, manners or events in personal life (e.g. break-up with boyfriend/girlfriend) may lead to unpredictable and destructive retaliatory behaviour, self-depreciation, depression and etc.
Meanwhile, the websites can be used either for already discussed online diaries (blogs) or for putting any other type of information: kids adore joining various fan clubs of favorite celebrities, games, TV shows, music and so on. However with the various malicious intensions, they can create websites, which are specifically designed to offend another child or group of children. And even worse – they can post personal information and photos, which increases risk for victims to be found or contacted (remember that sexual offenders are often interested in such kind of information).
5. Malicious Online Impersonation. Sometimes cyberbully, in order to deceive, may pretend to be someone else online and this is called online impersonation. Actually it can bring just as much damage as any other way of cyberbullying, because pretender may do the following:
- send insulting, hateful messages to victims family members, friends or to other know or unknown people;
- send provocative messages to victim’s enemies and organize confrontation with them by giving the victim’s contacts (name, address, mobile number);
- alter a real victim’s message to make it look that he/she said something inappropriate or very personal.
For an obvious reason to convince others that it is not victim’s fault might be very tricky after all.
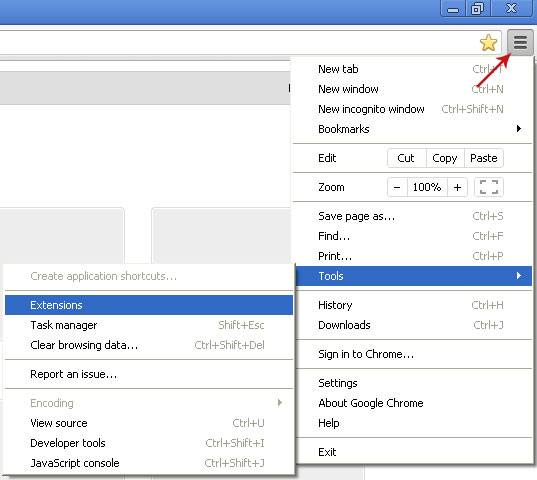
6. Stealing passwords. Many password hacking programs are available online and might be used by any child for stealing another child’s password. In the meantime having a victim’s password, even it is only his/her social network account password, means a lot. First of all, the bully can edit victim’s profile information by adding offensive or inappropriate information. Later these changes may become an object of derision, humiliate victim or just attract unwanted attention. Secondly, stolen account can be used for chatting with familiar or unfamiliar people and saying nasty things to them. They may become really angry and they won’t even realize that they are talking with other person. And thirdly, children may sometimes decide to lock or delete stolen accounts, which also upsets and flusters their owners. Moreover, once password is stolen and published, other hackers may try to hack into victim’s computer too.
7. Internet Polling. Internet pool is another way to "bully" your child online. In fact, it is a perfect place to create rumors and offensive questions: Who is the ugliest person in the class? Who’s a Slut? Who’s Not? While kids poll to answer, another one may feel really embarrassed or humiliated.
8. Interactive Gaming. Surprisingly, playing interactive games on video game consoles (e. g. PlayStation, Xbox) might become a place for bullying too. The fact is that these gaming devices allow playing online and chatting with chosen or matched player. However when children get very involved in the game, they often become aggressive towards their opponents and start using threats and lewd language. Sometimes it may go even further: they are creating false rumors, stealing their accounts or throwing them out of the game.
Cyberbullying by proxyAs it has been already mentioned above, cyberbullying through proxy is simply indirect bullying, i.e. when the bully uses accomplices to perform his planned malicious operations. Actually, the person, who gets involved in such kind of cyberbullying, rarely realizes that he/she is doing the dirty work. However the most dangerous situations arise when the adults are involved, especially the sexual abusers or the ones, who are unaware that they are dealing with child. And, unfortunately, it happens very often. Therefore the cyberbullying by proxy is considered as the most dangerous kind of cyberbullying. In order to recognize it, the most frequent situations are described below, but keep in mind that the variety of such attacks is nearly endless.
One of the simplest examples of indirect cyberbullying is "Warning wars". Many ISP (Internet service providers) provide the possibility to report the user, which is using inappropriate language and thus violating their rules. However some children use the warning buttons on their email, chat or IM screens just in order to eliminate other children from chat or make them lose their accounts. Of course, the service provider firstly checks the validity of these warnings, but cyberbullies know that and therefore they provoke their victims to say something rude or nasty back. It is needless to say what goes next. The service provider gets a proof and becomes an innocent accomplice of the bully by blocking or stopping the victim’s account. Very similar situation may happen with victim’s parents too. The cyberbully can make it look like the victim had started bullying and when parents notice that (or are notified) they blame their kids and punish them without realizing that they are wrong.
Another way to start cyberbullying by proxy is to pose as the victim and thus to make a lot of problems to him/her. The cyberbully can create a new account or control the existing victim’s account (by hacking into it or simply stealing the password), but however they do it, the main aim is to send many offensive, nasty and rude messages to victim’s friends, known and unknown people. These people usually get angry and disappointed with the victim without knowing who they are really speaking with. The worst thing is that the victim can neither prove himself/herself innocent nor stop it, especially if the bully have changed the account password.
Sometimes posing as the victim can be used in other way and involve more people. For example, Thom gets angry at his classmate Tiffany, because she didn’t invite him to her birthday party, and therefore he decides to seek revenge. Thom goes to any buddy profile website and, posing as Tiffany, posts "Thom is the ugliest and the dumbest boy in the word, I want to see him dead" or something even more offensive and humiliating. Then the boy begins playing the victim: he starts blaming the girl for being mean, shows the post to Tiffany’s friends, teachers or parents and makes them do his dirty work. In the end Thom looks like the "good guy" and, on the contrary. Tiffany, being completely innocent, has a lot of problems: she may be punished by her parents, get into trouble at school and lost her friends.
Unfortunately, cyberbullying may go even further than that. Sometimes for faster and better result, the bully posts information about the victim or pose as a victim in hate group chat rooms, child molester chat rooms and/or on their discussion boards. They also publicize the personal and contact information about the victim, hoping that the members of hate group or child molester group will contact and attack the victim online or even offline. And they do. People, feeling insulted or attracted (depends on the group type), start calling, sending threats and hateful messages or simply seek to meet the victim face to face. The last action can be extremely dangerous and result in serious physical injuries. Therefore, if you are receiving similar death threats from unknown people, immediately tell about it for your parents and call the police.
Preventing CyberbullyingIn order to avoid or prevent cyberbullying, follow the recommendations written below. Notice that actions, which may be taken in one or another situation, may vary according to the type of cyberbullying.
Mobile messaging (text, pictures, videos). First of all, try to avoid sharing your mobile phone number with everyone, especially with barely known people. You should also consider entering your number on popular websites (such as Facebook, Twitter, etc.) or instant messengers (Skype, Windows Messenger, etc.), because then your number may become available to all your contacts or even publicly. And more, be careful when leaving your phone unsupervised and reachable for everyone as it may be the way to get your contacts too.
However, if the cyberbully has got your number already and now you are suffering from abusive text messages or obscene pictures/videos, try to calm yourself down and don’t write anything back to the bully. Angry response won’t resolve anything - actually, the situation may become even worse after that. The best thing you can do is to report abusive messaging for your mobile service provider (Vodaphone, Orange, T-mobile, etc.) and they will block specific numbers from calling/texting to you. Check their websites for more information.
Online Messaging (through chatrooms, instant messengers). A primary way to protect yourself from potential cyberbully, while chatting online, is to keep your personal information concealed. Even the nickname should be chosen so that no one would be able to recognize your real name, location, age or any other actual information. Of course, some people may still post something offensive or humiliating to you in the chatroom or through instant messenger, but at least you will be sure that the bully won’t reach you directly and won’t leave thousands of unsolicited messages in your mailbox box or on your mobile phone.
But still, if you have received abusive post or message, simply ignore it and do not start replying anything back. It has been written above already, how to deal with rude text messages and actually, the same stands for online chatting – being calm and ignoring is the best way to avoid more problems. You may even log off, if you feel like you can’t stand it anymore. And moreover, think about what you write too. Online chatting is not the same as direct conversation and, therefore, it is easier to misunderstand what you actually meant. Reckless words may provoke the conflict and conflict is sometimes the begging of cyberbullying.
Emailing. Emails are used for communication through the Internet and usually are absolutely harmless. However, it can also be easily used for cyberbullying. Therefore if you receive a threatening or humiliating email, or even worse, several emails, you should know how to deal with them.
The first and the most important rule – never respond to such kind of emails, but save or print them. The fact is that the sender is actually seeking your attention and when he/she gets it, he/she feels satisfied and probably will start even more aggressive bullying. On the contrary, ignoring their letters may reduce or even stop the bullying. However simply deleting these letters may be not the best solution either. In some cases, you may need evidence that you have received something and therefore it is recommended to save them.
If the bullying continues, even though you haven’t replied to it, then you should try to identify the sender. If you are using an email client, such as Outlook or Outlook Express, press the right mouse button over an email and you will get detailed information about from where/whom the letter arrived. Then you may ask your parents for help in contacting the school or service provider of the sender’s email.
Of course, emails can also be sent anonymously or from the person that is absolutely unknown (spamming). Companies or individuals use the email harvesters or other special computer programs to obtain many random email addresses from the internet and then send messages to each of them (as a rule – automatically). Obviously, there is no need for you to reply to any of these letters. Sometimes, there might be a link, which is ostensibly supposed to stop spamming, but be aware, that it is only a trick. Actually by clicking such kind of links, you only confirm that your email address is real and in use, so after that you can expect even more active email flooding, especially when your address is sold or passed to other people.
So what to do if you are constantly getting junk and abusive messages from different emails? Well, probably this problem has only two solutions. The first one is to separate normal emails from junk, because blocking or stopping in such situation is practically impossible (too many senders). For doing this, check the possibilities of your email program - many of them offer filter functions and are able to redirect the spam to another folder. Of course, this won’t solve the actual problem, but at least you will be shielded from it. The second solution, unfortunately, is to delete your current email account and to create a new one. In any case, this is a way better then reading or deleting spam every time you log in.
Websites. Sometimes cyberbullying begins on the school or community page, but not necessarily, nasty information can be posted in any website. In the first case, you should tell someone about it. This can be your parents or teachers, just according to the situation. However the second case requires a little bit more efforts - you should find out who hosts that website at first. There are some good articles on the Internet, where you can read about it. For example, take a look at the Bully OnLine website, which not only reveals how to get more information about the possible website owner, but also talks about general online safety.
Google Yourself and Your KidsWell, it probably sounds like a joke, but actually you might be surprised how much Google “knows” about you and your personal life. The fact is that Google is the search engine and collects any pieces of information available online. Therefore, you can try to “Google” yourself or someone else, i.e. to use Google for searching any kind of information about yourself or any other person. Unfortunately, this means that others can “Google” you too.
You may be still wondering why the information about you is available online and how does it happen. Actually, in many cases it is our own fault. You will probably agree that nowadays more and more of us are using the Internet. We are communicating, sharing our ideas or simply checking the information and news posted by others. Therefore lots of personal information is posted online. Maybe you have created an account in any of social networking websites and filled in some information about yourself? Maybe you have signed up in any other website and incautiously accepted the privacy rules? Maybe you have posted something in the public forum or just written a post about your personal experience or opinion? Or maybe your children have shared any similar information with others?
In fact, every single detail ever written online might be reached by others. Therefore think twice before sharing any personal information online, because the consequences might be very unpleasant. For example, just imagine if you post your contact information (such as telephone number or address) online. It practically means that everyone can reach it now and one day you can meet uninvited guest just in front of your door. Who knows what that stranger can do to you and your family? And are you sure that your child haven’t posted this kind of information yet?
So now it is more or less clear how Google “gets” information about you and how dangerous it can be. The good thing is that you can control it, but before that try to „Google“ yourself, your kids and other family members at first. By doing this you will realize how much and what kind of information is available online about you and them.
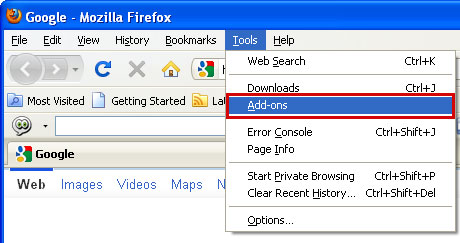
In order to begin, launch
Google in your web browser. Then type your real name and surname in quotes, e.g. “Name Surname” and click Google search. All the results, you see in the window, is the information relating you or the people, which have the same name and surname like yours. Then you can try to type your full e-mail address (e.g. name.surname@email.com), nick name, mobile or telephone numbers, street address or other personally identifiable information. The same search should be repeated in sections: „images”, “groups” and “news”, even though the last one is mostly about public figures. And don’t forget quotation marks, if you are searching for specific phrase of two or more words and want that this phrase would be searched as a whole and not picked apart by Google.
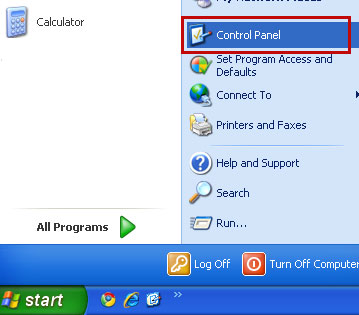
After “Googling” yourself, your kids and other family members, make the final evaluation. Do you feel like too much information is available online? Is there anything, you don’t want to be known by others? Well, at first you should contact Google and ask them to erase this information. But in many cases you would also need to make a request to the site or online service, where unwanted content is posted.
This, probably, seems to be very easy, but actually it isn’t. Some site founders don’t really care about what is posted in their pages, especially when they day by day receive a lot of new posts (for example, discussion boards). However many of them will react, when their terms of service (TOS) are violated. So there is the point from which you should start. Read the TOS for the site, where the information is posted, and try to find a violated rule. Maybe publishing information of other persons is not allowed without their permission? Or maybe posting any personal or inaccurate information is prohibited? In other words, if the information posted in site, violates any of TOS, the hosting company is more likely to remove it.
Of course, in order to achieve such reaction, you have to contact the right person at first. The easiest way is to write to the webmaster, because their emails usually are very simple: webmaster@[the Website name/URL], for example “webmaster@website.com”. Also, check the privacy contact at the site or a DMCA contact, which is related with copyright violations and therefore often reviewed. In your email, you should clearly describe the problem: introduce and prove yourself as a person, whose information is published, copy the URL of the page where this information is placed and finally specify which information exactly should be deleted. Wait for the answer about a week or two, and then send a kind reminder with the date, when earlier e-mail was sent. If still no response, after a week or two, send an email to privacy@wiredsafety.org. Also, when the issue concerns your kids under the age of thirteen, you can contact
COPPA (the Children’s Online Privacy Protection Act) or
FTC directly (http://www.ftc.gov). These organizations are very carefully enforced and will immediately react. You may be asked to prove that you are the parent, but as soon as you prove it, the information from website will be removed.
A slightly different letter has to be written, when you are worried about inaccurate information posted by you or someone else. It is usually a bit more complicated to change the part of the post than remove it entirely and some websites can only remove the old post and repost the new, correct information (some can’t do even that). Therefore it would be better if you include correct information in the e-mail in advance (before sending it).
The special actions should be taken if you find a site, which is related with children sexual harassment or cyberstalkers. Do not underestimate them, especially if they are trying to frighten you or your child. Strange calls at midnight or nasty posts offering you or your child for sex, is the signal that law enforcement must be involved. But they won’t be able to do anything if there would be no link to real offline contact information. In this case, the WiredSafety.org should be contacted.
What Parents Can Do?The first action to be taken, when you find out that your children are being cyberbullied, is to talk about it with them and, especially, about their feelings and fears. Moreover, make sure that you will support and protect them from any further accuses or threats.
After a conversation with kids, you should consider reporting this problem to your child school’s administration or teachers. Many schools and after-school clubs have their own means how to deal with cyberbulying, although they may vary according to the district or state. And moreover, always ask your child permission before contacting school, because he or she might be afraid about their friends’ reaction, taunting and so on and therefore it might be necessary to convince or calm him/her down at first.
Do not hesitate to contact a therapist or counselor at school if you see that you are not able to control the situation alone.
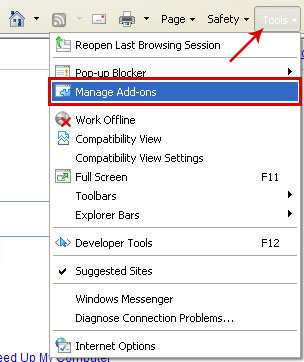
Other possibilities to prevent cyberbullying1. Blocking. It is probably the easiest way to stop unsolicited messages. Simply block the specific person from contacting your child by changing the settings of device (many of them have the block function).
2. Controlling activities. Usually children do not realize how dangerous is to share personal or contact information online. Therefore, you have to talk about it with them as soon as they start using Internet. The essence of privacy, strong passwords and internet ethics must be emphasized during that kind of conversation. Moreover, don’t forget to supervise your children online activities constantly.
3. Limiting access. Many children simply can’t stop checking messages in their phones, email boxes, messengers and elsewhere, even though these messages are nasty, humiliating and hurtful. Then limiting access to computer or mobile phone is probably the only way to significantly reduce or eliminate cyberbullying, even though it may upset your child.
Cyberbully: The movieCyberbully. Part 1
Cyberbully. Part 2
Cyberbully. Part 3
Cyberbully. Part 4
Cyberbully. Part 5
Cyberbully. Part 6
Share this information with your friends: