The motivation for malware creators is profit. Do not pay for System Security 2011. If you've already bought it, please contact your credit card company and dispute the charges. You should also consider closing your current credit card and creating a new one. Cyber crooks may sell your credit card information on the underground forums. And finally, please follow the removal instructions below to remove System Security 2011 and associated malware from your computer. It's worth mentioning that System Security 2011 may come bundled with a rootkit. Rootkit is a are very sophisticated malware and may block legitimate anti-malware products. It is wise to run a rootkit removal tool before using anti-malware or anti-virus scanner. Hopefully, I made it a bit clear. Now, as you know what's going on, please follow the steps in the removal guide below very carefully. Especially the alternate manual removal guide, if you choose to remove this virus manually. Last, but not least, if you need any help, please leave a comment below. Good luck and be safe online!
Here's what the rogue antivirus called System Security 2011 looks like. Unique design, looks like an iPad to me :)

A couple of fake security alerts you may see when this rogue antivirus is active.


By far the most easiest way to get rid of System Security 2011 is to use the debugged activation code 9992665263 and run anti-malware software.
http://deletemalware.blogspot.com
System Security 2011 removal instructions:
1. First of all, download and run ZeroAccess/Sirefef/MAX++ removal tool. (works on 32-bit systems only!)
2. Then use TDSSKiller.
3. And finally, download free anti-malware software from the list below and run a full system scan.
NOTE: in some cases the rogue program may block anti-malware software. Before saving the selected program onto your computer, you may have to rename the installer to iexplore.exe or winlogon.exe With all of these tools, if running Windows 7 or Vista they MUST be run as administrator. Launch the program and follow the prompts. Don't forget to update the installed program before scanning.
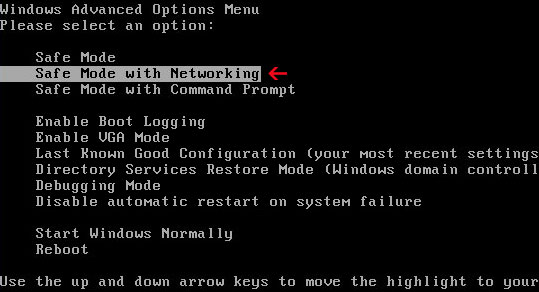
If you can't download it, please reboot your computer is "Safe Mode with Networking". As the computer is booting tap the "F8 key" continuously which should bring up the "Windows Advanced Options Menu" as shown below. Use your arrow keys to move to "Safe Mode with Networking" and press Enter key. Open Internet Explorer and download STOPzilla. Once finished, go back into Normal Mode and run it. That's It!
Read more detailed instructions here: http://www.computerhope.com/issues/chsafe.htm
NOTE: Login as the same user you were previously logged in with in the normal Windows mode.
Manual System Security 2011 removal guide:
1. Right-click on System Security 2011 icon and select Properties. Then select Shortcut tab.
The location of the malware is in the Target box.
2. In our case the malicious file was located in C:\Windows\System32 folder. Select the malicious file, rename it and change a file name extension.
Original file: TcS22bF3nGaQWKf.exe

Renamed file: TcS22bF3nGaQWKf.vir

3. Restart your computer. After a reboot, download free anti-malware software from the list below and run a full system scan.
4. Download free anti-malware software from the list below and run a full system scan.
NOTE: in some cases the rogue program may block anti-malware software. Before saving the selected program onto your computer, you may have to rename the installer to iexplore.exe or winlogon.exe With all of these tools, if running Windows 7 or Vista they MUST be run as administrator. Launch the program and follow the prompts. Don't forget to update the installed program before scanning.
5. Remove the TDSS/ZeroAccess rootkit (if exists). Please follow this removal guide: http://deletemalware.blogspot.com/2010/03/tdss-alureon-tidserv-tdl3-removal.html
Manual activation and System Security 2011 removal:
1. Choose to remove threats and manually activate the rogue program. Enter one of the following codes to activate System Security 2011.
9992665263
1148762586
1171249582
1186796371
1196121858
1225242171
1354156739
1579859198
1789847197
2. Download free anti-malware software from the list below and run a full system scan.
NOTE: in some cases the rogue program may block anti-malware software. Before saving the selected program onto your computer, you may have to rename the installer to iexplore.exe or winlogon.exe With all of these tools, if running Windows 7 or Vista they MUST be run as administrator. Launch the program and follow the prompts. Don't forget to update the installed program before scanning.
3. Remove the TDSS/ZeroAccess rootkit (if exists). Please follow this removal guide: http://deletemalware.blogspot.com/2010/03/tdss-alureon-tidserv-tdl3-removal.html
Associated System Security 2011 files and registry values:
Files:
- C:\WINDOWS\system32\[SET OF RANDOM CHARACTERS].exe
- C:\Documents and Settings\[UserName]\Application Data\csrss.exe
- C:\Documents and Settings\[UserName]\Application Data\hTrkd58DeORldrQSystem Security 2011.ico
- C:\Documents and Settings\[UserName]\Application Data\Microsoft\csrss.exe
- C:\Documents and Settings\[UserName]\Desktop\System Security 2011.lnk
- C:\Documents and Settings\[UserName]\Local Settings\Temp\[SET OF RANDOM CHARACTERS].tmp
- C:\Documents and Settings\[UserName]\Start Menu\Programs\System Security 2011\System Security 2011.lnk
- HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run "[SET OF RANDOM CHARACTERS]"
No comments:
Post a Comment