We all know about computer viruses and while they are indeed a huge nuisance there is actually an even bigger reason to be worried about the information we have on our PC's and laptops. You may or may not have heard of 'ransomware' – or as it can also be known: Trojan ransom, cryptotrojans and scareware. None of them sound particularly friendly and that's because they're not!
So what is FBI Cybercrime Division ransomware virus, how does it worm its way onto our computers and how can we fix the problem if we are unlucky enough to become a victim of this virus?

Ransomware is pretty much as the title suggests: it infects your computer then holds your files ransom and asks for money to release them. Unlike regular computer viruses, ransomware is known as a 'drive-by' virus, which means that instead of it installing its malicious software on your PC when you click on an infected email attachment or file, it can be installed simply by you having visited a website that has been compromised. Of course, I'm not saying that 'drive-by' downloads are responsible for all infections and indeed this virus may be distributed via spam or infected websites, it's just from what I've seen so far, 'drive-by' downloads are in a leading role.

There are two basic forms of ransomware; as mentioned the one above which will encrypt your files and documents and then demand payment for providing the decryption code or key. The other is, if anything, even more sinister as it pretends to have originated from the police. Known as police themed ransomware, depending on your home country, you may be held to ransom by criminal hackers pretending to be the FBI, the UK's Metropolitan Police Force or another similar organization across Russia or Europe. Since I live in the United States, the infection takes my IP address and loads the FBI. Cybercrime Division warning. But if let's say you live in Europe, UK then you will probably see the United Kingdom Police themed worning, either Police Central e-crime Unit or Metropolitan Police.
In fact ransomware and this form of online extortion was believed to have originated in Russia but it soon spread to other parts of the world with some criminal groups believed to be making as much as $54,000 in US dollars in a single day. It's big business! And like any lucrative way of making easy money, the problem is not going to go away; if anything hackers are becoming increasingly sophisticated in their attempts to part you with your hard earned cash. Let's take a closer look at police-themed ransomware. Imagine you're sitting at home innocently reading the news online or browsing eBay when suddenly your computer freezes and a page pops up, purportedly from the FBI or the national police force in your country, telling you that you have been caught viewing under age porn or illegally downloading software, music, movies or your favourite TV show.
Of course, you panic – this is the Federal Bureau of Investigation as far as you're aware – and when they show you a list of penalties for your 'crime' and tell you that by paying a fine you will not have criminal charges pressed against you (and your computer will be unfrozen) then the temptation to freak out and pay up can be overwhelming. FBI Cybercrime Division virus even has the ability to turn on your laptop's webcam and will snap your picture and display it on your screen in an attempt to further enforce the illusion that you are being watched or recorded. Pretty terrifying stuff!
And of course, if you don't pay, then what? You fight the FBI to clear your name? After all, you've never downloaded anything illegal or watched illegal adult material. But how does one go about doing such a thing – and anyway, what about your computer and all of your files which are now frozen and completely inaccessible?
Ransomware certainly preys on our vulnerability, whether we're convinced we're completely innocent or are now panicking about that illegal download of the latest Hollywood blockbuster but the key thing to remember is that both the FBI in the United States and the Metropolitan Police Force in the UK have stated that they would never ask citizens to pay to unlock their PC, decrypt their files or pay an online penalty in this fashion.
So what should you do if this happens to you and your computer suddenly locks and you receive a message or a pop up page that is supposedly from a law enforcement agency saying "Your computer has been locked"? Unfortunately malicious software of this type is typically rather difficult for the regular home PC user to remove from their machine but I wrote a step-by-step guide on how to remove FBI Cybercrime Division virus, so hopefully you will be able to fix it yourself. Please note that, this ransomware infection is not the same for everyone. What works for you, may not work for other user and vice versa.
The other crucial thing to remember is to regularly back-up your files – malware of this nature can not only encrypt your files - sometimes beyond redemption - but can steal them too. Make backing up something you do on a regular basis and do everything you can in the fight against police-themed ransomware. And of course, use decent antivirus software and make sure it's always updated.
To remove this ransomware virus from your computer, please follow the removal instructions below. Do you have something to say about dealing with ransomware? Post your comment or question below.
Written by Michael Kaur, http://deletemalware.blogspot.com
FBI Cybercrime Division virus removal instructions using System Restore in Safe Mode with Command Prompt:
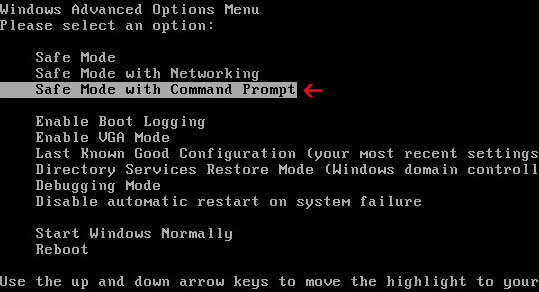
1. Reboot your computer in "Safe Mode with Command Prompt". As the computer is booting tap the "F8 key" continuously which should bring up the "Windows Advanced Options Menu" as shown below. Use your arrow keys to move to "Safe Mode with Command Prompt" and press Enter key.
2. Make sure you log in to an account with administrative privileges (login as admin).
3. Once the Command Prompt appears you have few seconds to type in explorer and hit Enter. If you fail to do it within 2-3 seconds, the ransomware virus will take over and will not let you type anymore.
4. If you managed to bring up Windows Explorer you can now browse into:
- Win XP: C:\windows\system32\restore\rstrui.exe and press Enter
- Win Vista/Seven/8: C:\windows\system32\rstrui.exe and press Enter
6. Download recommended anti-malware software (direct download) and run a full system scan to remove the FBI Cybercrime Division International Cyber Security Protection Alliance virus from your computer.
No comments:
Post a Comment