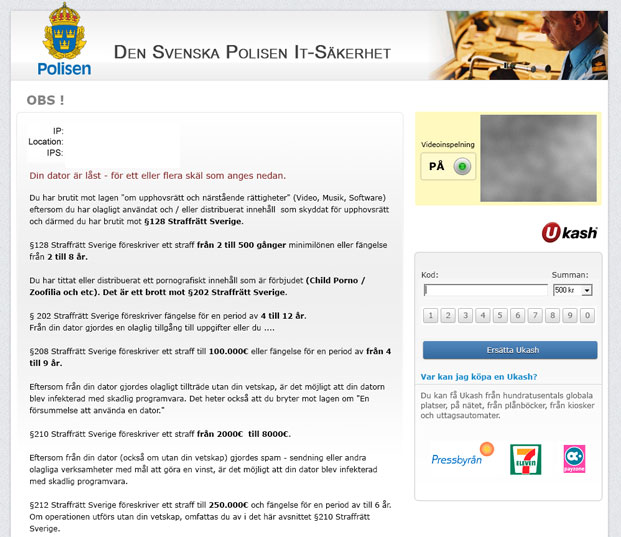
Den Svenska Polisen IT-Sakerhet and other similar
ransomware have been targeting Sweden computers with online extortion attacks at least for a few years. But it's happening more and more. New variants of ransomware are more sophisticated that most screen locking malware. They use advanced geo location tools, encrypted connections and even valid software certificates. Cyber crooks can now target users in specific cities rather than the whole country.
Sweden is one of the wealthiest countries in the world, no wonder it remains the main target for most cyber crooks. Besides, Swedes respect the laws and they have enough money to pay a 'fine'. The Swedish mentality is a key factor here, because they are usually socially closed, they hold the distance and are rather shy. They would rather react to the threat and pay the money than tell someone about it.
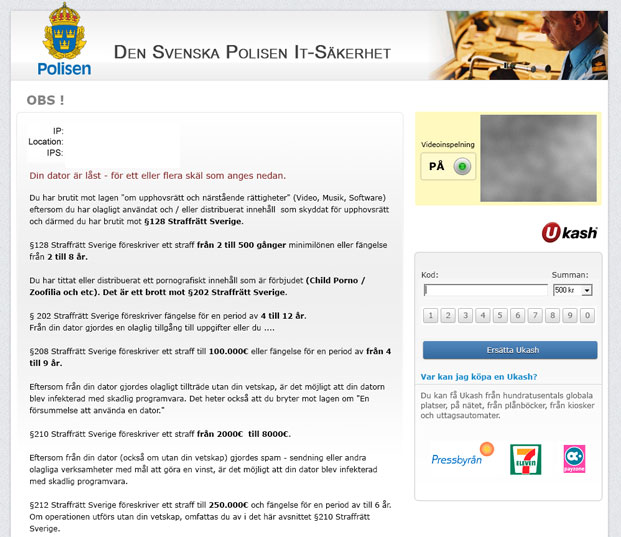
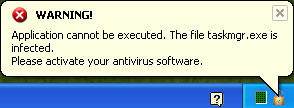
Police in Sweden are warning internet users not to pay a 'fine' via a prepaid money card or online payment services. Still, Police officers get dozens of complaints every day. A significant part of internet users in Sweden are not aware of ransomware. There are at least five different ransomware families targeting Sweden: Reveton, Gimemo, LockScreen, Ulocker and Weelsof. A ransom Trojan from any of these families instantly locks the infected computer. Bogus messages are slightly different but they all claim the user violated federal law by downloading or distributing copyrighted and illegal files. For example, the bogus warning message of Reveton malware looks like it's from the Svenska Polisen IT-Sakerhet. Other variants pretend to be from International Police Association Sweden and Polisen enheten för databrott.
To unlock the machine, the victim is told to pay a 'fine', about 500 kr. via Ukash. If the demands were not met, criminal charges would be filed and victim's machine would remain locked on that Polisen warning screen. The truth is, it will remain locked no matter if you pay a 'fine' or not. This part is not very important for cyber crooks. They got the money, so why bother?
If you think that such attacks, especially in Sweden are not successful then think again. From 3 to 5 percents of infected users choose to pay a 'fine'. Only a few other countries have such high conversion rates. Let’s do the math, 1000 infected PCs, 50 users who sent the money (usually $100) and we have $5000 a day. Not bad, right?
One of our readers got the Den Svenska Polisen IT-Sakerhet virus when he visited one of his favorite adult sites. Another user said he got if from an online games site. We took a look at both sites. The first one is a well known adult site ranking very well in Sweden. Our reader said it wasn't the first time he got a virus from that site. It makes me wonder whether it's just a coincidence or the owner of investigated adult site has some sort of agreement with cyber crooks. As for the online games site it's rather new, just about two months old. However, it already has an amazing number of back links which is probably the main reason why the site went from zero to the second page in just a few months. On both cases, the infection was delivered by a 'drive-by' download. This is why good security software is a must. Also, it's a good idea to back your files because certain variants of ransomware encrypt the files using rather strong encryption and there’s really no way for an average PC user to crack it.
To remove Den Svenska Polisen IT-Sakerhet Ukash virus ransomware, please follow the removal instructions below. Feel free to comment if you have any questions or need help removing this malware. Good luck and be safe online!
http://deletemalware.blogspot.com
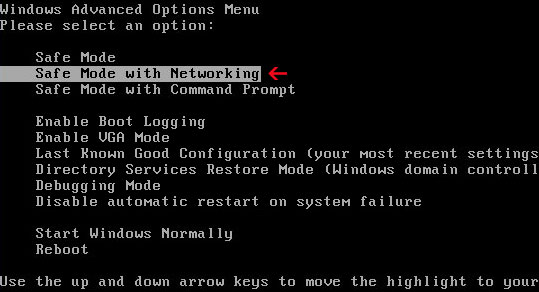
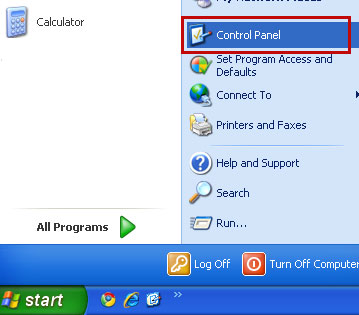
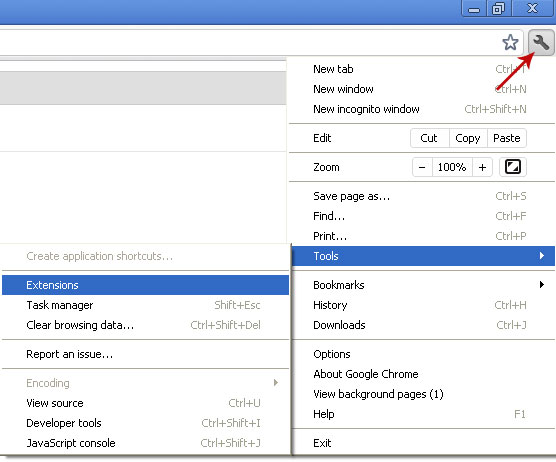
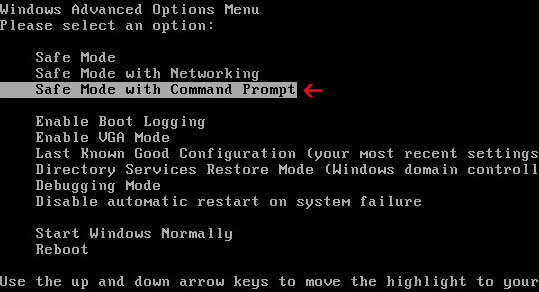
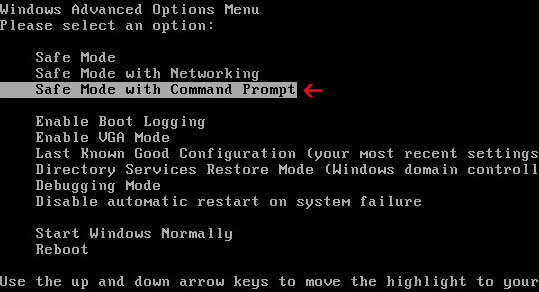
Quick Den Svenska Polisen IT-Sakerhet Ukash removal instructions (System Restore, may not work for all users):1. Unplug your network cable and manually turn your computer off. Reboot your computer is
Safe Mode with Command Prompt. As the computer is booting tap the
F8 key continuously which should bring up the
Windows Advanced Options Menu as shown below. Use your arrow keys to move to Safe Mode with Command Prompt and press Enter key.
2. Make sure you log in to an account with administrative privileges (login as admin).
3. Once the Command Prompt appears you have few seconds to type in
explorer and hit Enter. If you fail to do it within 2-3 seconds, the Den Svenska Polisen IT-Sakerhet ransomware will take over and will not let you type anymore.
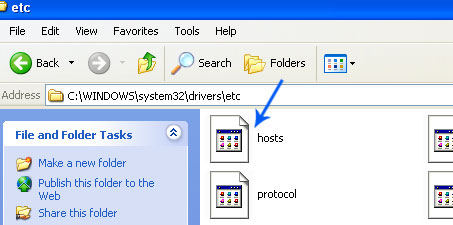
4. If you managed to bring up Windows Explorer you can now browse into:
- Win XP: C:\windows\system32\restore\rstrui.exe and press Enter
- Win Vista/Seven: C:\windows\system32\rstrui.exe and press Enter
5. Follow the steps to restore your computer into an earlier day.
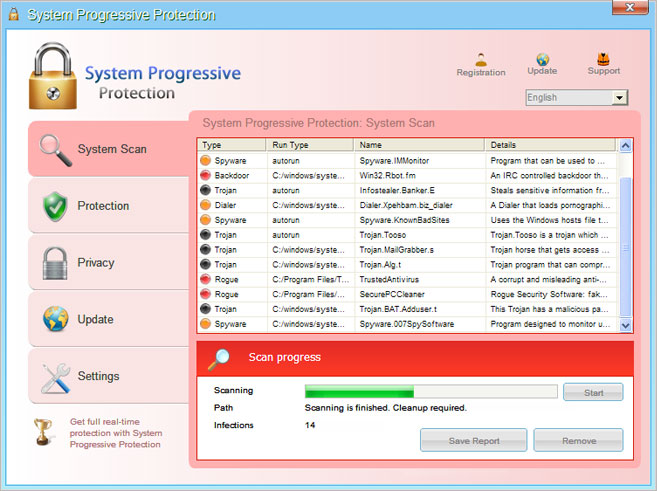
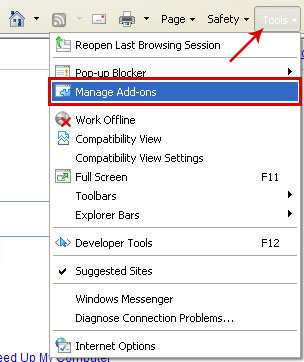
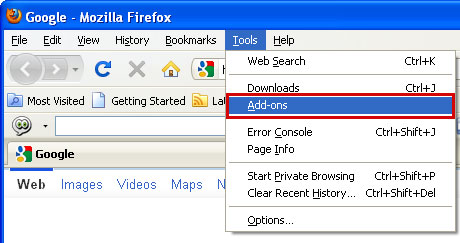
6. Download recommended
anti-malware software (direct download) and run a full system scan to remove the remnants of Den Svenska Polisen IT-Sakerhet ransomware.
Den Svenska Polisen IT-Sakerhet ransomware removal using Kaspersky Rescue Disk:1. Download the
Kaspersky Rescue Disk iso image from the Kaspersky Lab server. (
Direct download link)
Please note that this is a large downloaded, so please be patient while it downloads.
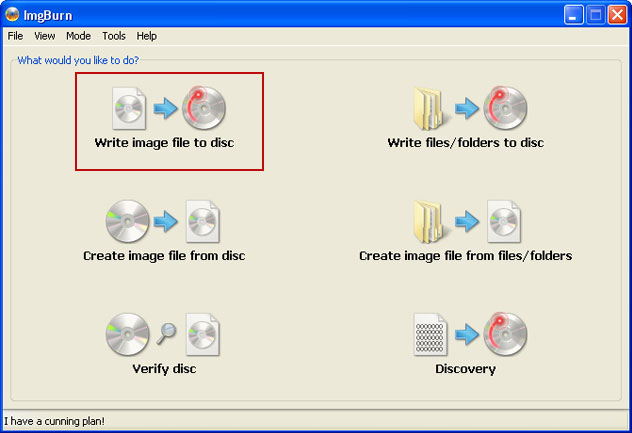
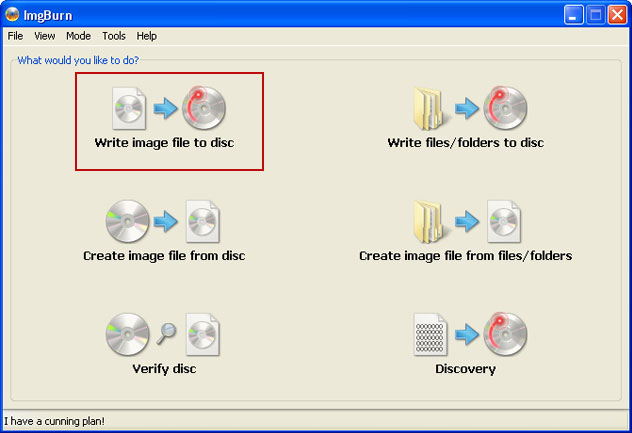
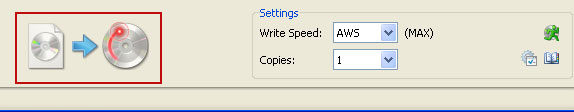
2. Record the Kaspersky Rescue Disk iso image to a CD/DVD. You can use any CD/DVD record software you like. If you don't have any, please download and install
ImgBurn. Small download, great software. You won't regret it, we promise.
For demonstration purposes we will use ImgBurn.
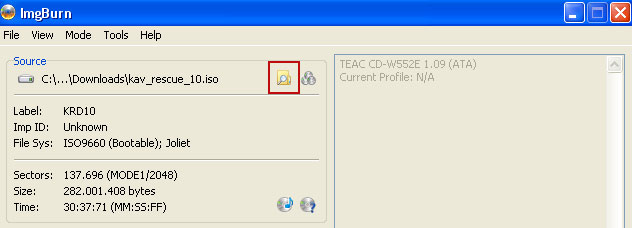
So, open up ImgBurn and choose
Write image file to disc.
Click on the small
Browse for file icon as show in the image. Browse into your download folder and select
kav_rescue_10.iso as your source file.
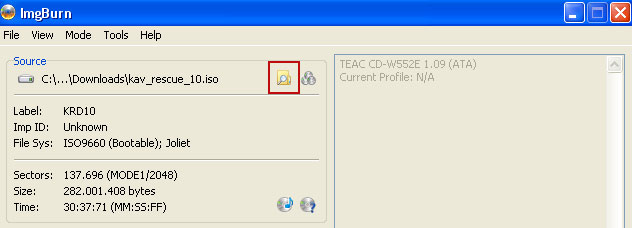
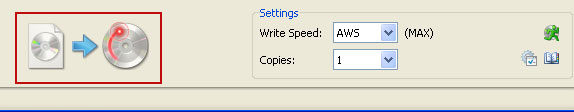
OK, so know we are ready to burn the .iso file. Simply click the
Write image file to disc button below and after a few minutes you will have a bootable Kaspersky Rescue Disk 10.
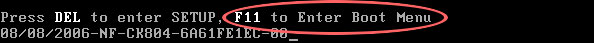
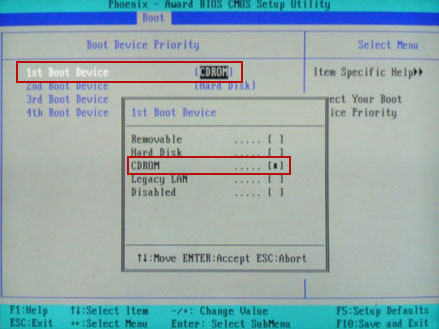
3. Configure your computer to boot from CD/DVD. Use the
Delete or
F2,
F11 keys, to load the
BIOS menu. Normally, the information how to enter the BIOS menu is displayed on the screen at the start of the OS boot.
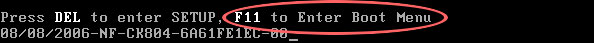
The keys F1, F8, F10, F12 might be used for some motherboards, as well as the following key combinations:
- Ctrl+Esc
- Ctrl+Ins
- Ctrl+Alt
- Ctrl+Alt+Esc
- Ctrl+Alt+Enter
- Ctrl+Alt+Del
- Ctrl+Alt+Ins
- Ctrl+Alt+S
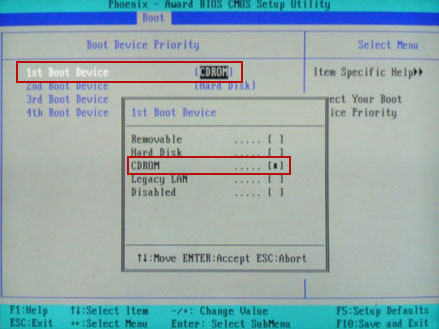
If you can enter
Boot Menu directly then simply select your CD/DVD-ROM as your
1st boot device.
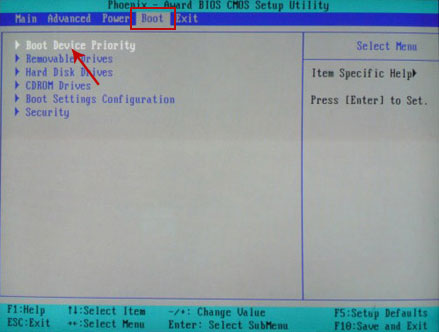
If you can't enter Boot Menu directly then simply use
Delete key to enter
BIOS menu. Select
Boot from the main BIOS menu and then select
Boot Device Priority.
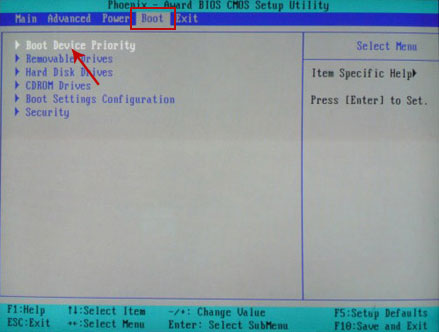
Set CD/DVD-ROM as your
1st Boot Device. Save changes and exist BIOS menu.
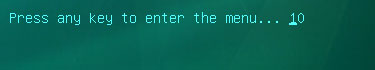
4. Let's boot your computer from Kaspersky Rescue Disk.
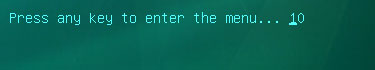
Restart your computer. After restart, a message will appear on the screen:
Press any key to enter the menu. So, press
Enter or any other key to load the Kaspersky Rescue Disk.
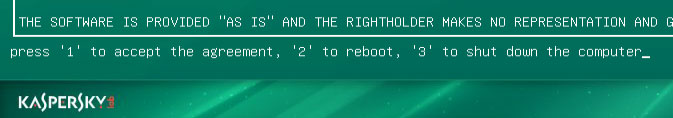
5. Select your language and press
Enter to continue.

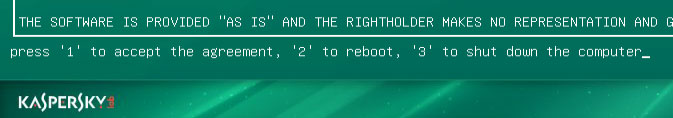
6. Press
1 to accept the End User License Agreement.
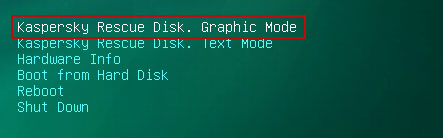
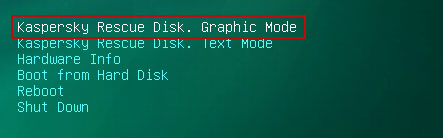
7. Select
Kaspersky Rescue Disk. Graphic Mode as your startup method. Press
Enter. Once the actions described above have been performed, the operating system starts.
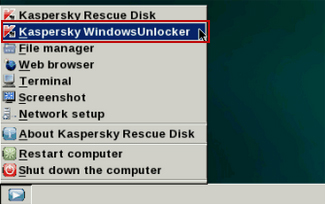
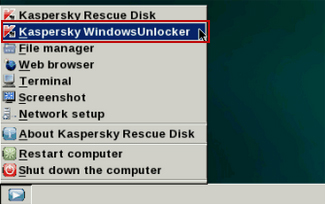
8. Click on the
Start button located in the left bottom corner of the screen. Run
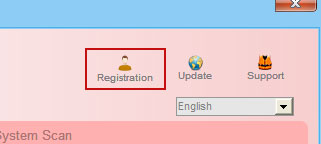
Kaspersky WindowsUnlocker to remove Windows system and registry changes made by Den Svenska Polisen IT-Sakerhet ransomware. It won't take very long.
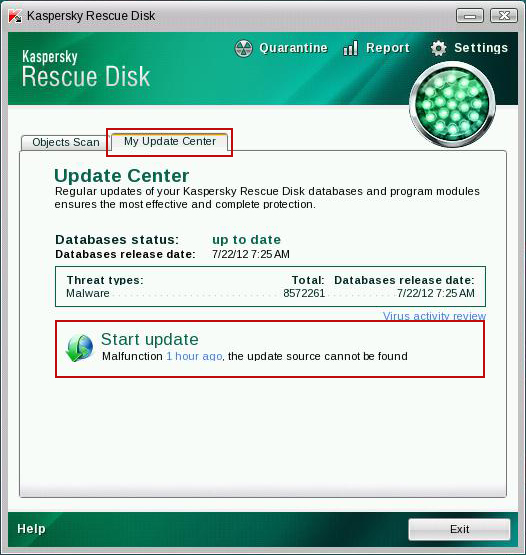
9. Click on the
Start button once again and fire up the
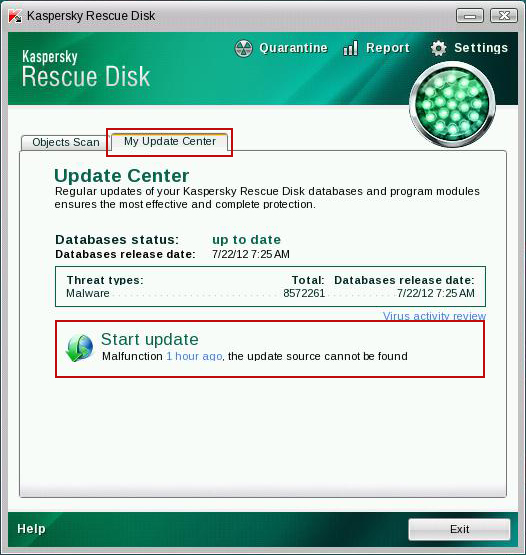
Kaspersky Rescue Disk utility. First, select
My Update Center tab and press
Start update to get the latest malware definitions. Don't worry if you can't download the updates. Just proceed to the next step.
10. Select
Object Scan tab. Place a check mark next to your local drive C:\. If you have two or more local drives make sure to check those as well. Then click
Start Objects Scan to scan your computer for malicious software.

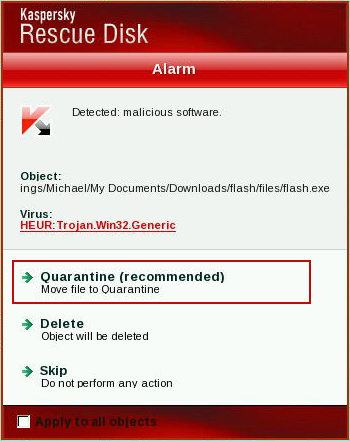
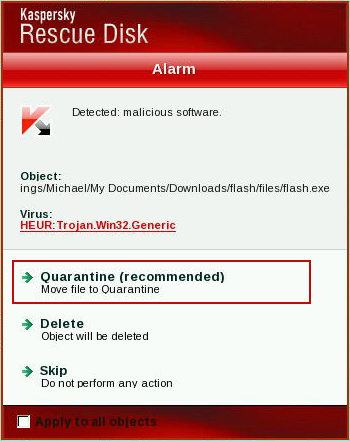
11.
Quarantine (recommended) or
delete every piece of malicious code detected during the system scan.
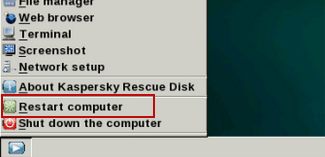
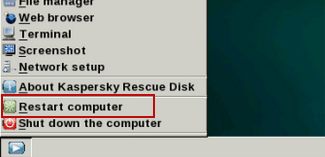
12. You can now close the Kaspersky Rescue Disk utility. Click on the
Start button and select
Restart computer.
13. Please restart your computer into the
normal Windows mode. Download recommended
anti-malware software (direct download) and run a full system scan to remove the remnants of Den Svenska Polisen IT-Sakerhet ransomware and spyware modules.
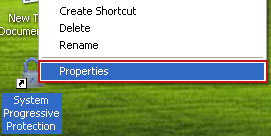
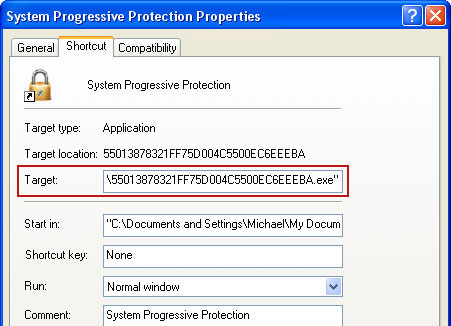
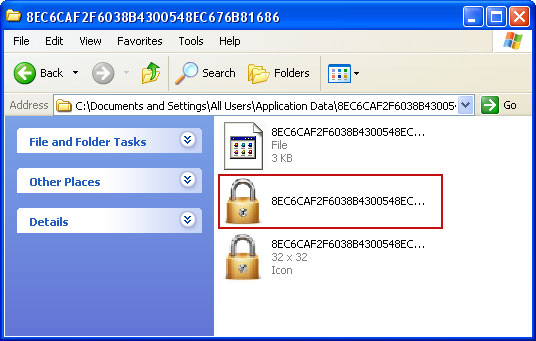
Associated Den Svenska Polisen IT-Sakerhet ransomware files and registry values:Files:
- [SET OF RANDOM CHARACTERS].exe
Registry values:
- HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon\"Shell" = "[SET OF RANDOM CHARACTERS].exe"
Tell your friends: