
As a typical rip-off rogue, WinDefrag will display fake pop-ups and error messages to scare you and to make you think that tour computer is seriously messed up. It will state that your hard drive is missing or that RAM memory usage is critically high. The text of some of the fake pop-ups you may see include:
Critical Error
Hard Drive not found. Missing hard drive.
Critical Error
Windows can't find hard disk space. Hard drive error
Critical ErrorWhat is more, it will block some of your programs saying Windows detected a hard drive problem:
A critical error has occurred while indexing data stored on hard drive. System restart required.
Windows detected a hard drive problem.Please note that if you attempt to run a program enough times it will eventually work. Win Defrag reports the same fake errors (usually 11 problems) of every infected computer. Some of the fake errors you may see:
A hard drive error occurred while starting the application.
Read time of hard drive clusters less than 500 msThankfully, Win Defrag is not the most aggressive rogue out there and you can remove it manually by deleting all temp files from C:\Documents and Settings\[User Name]\Local Settings\Temp (Local Settings folder is hidden by default so you will have to change folder options to see hidden files if you haven't already). Please follow the removal instructions below.
Bad sectors on hard drive or damaged file allocation table
Drive C initializing error
Hard drive doesn't respond to system commands
Data Safety Problem. System integrity is at risk.
Registry Error - Critical Error
If you have already purchased this bogus program then contact your credit card provider and dispute the charges and cancel your credit card because the scammers may sell you credit card information or use it again. If you have any questions or additional information about Win Defrag malware, please leave a comment. Good luck and be safe online!
Win Defrag removal instructions:
1. Open Task Manager (Ctrl+Alt+Delete).
2. Click on the Processes tab.
3. Click to highlight [SET OF RANDOM CHARACTERS].exe, e.g. 1938417.exe and click End Task. If it asks you "Are you sure you want to terminate the process?" click yes. This will stop WinDefrag.
4. Click to highlight explorer.exe and end it too. Then click the File -> "New Task (Run...)" from the menu on the bottom right. Type in explorer.exe and click OK.
5. Open directory:
C:\Documents and Settings\[UserName]\Local Settings\Temp (in Windows 2000/XP)
C:\Users\[UserName]\AppData\Local\Temp (in Windows Vista & Windows 7)
Delete all files from this directory.
NOTE: Local Settings folder is hidden by default so you will have to change folder options to see hidden files.
6. Download free anti-malware software from the list below and run a full system scan.
NOTE: in some cases the rogue program may block anti-malware software. Before saving the selected program onto your computer, you may have to rename the installer to iexplore.exe or winlogon.exe With all of these tools, if running Windows 7 or Vista they MUST be run as administrator. Launch the program and follow the prompts. Don't forget to update the installed program before scanning.
7. New threats appear every day. In order to protect your PC from such (new) infections we strongly recommend you to use ESET Smart Security.
Alternate Win Defrag removal instructions (in Safe Mode with Networking):
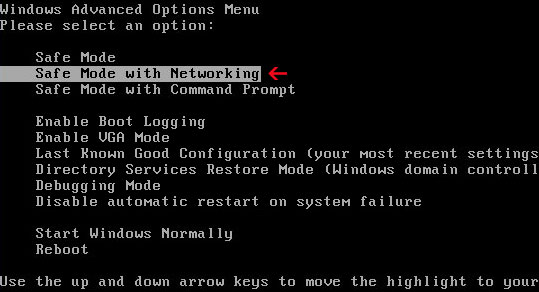
1. Reboot your computer is "Safe Mode with Networking". As the computer is booting tap the "F8 key" continuously which should bring up the "Windows Advanced Options Menu" as shown below. Use your arrow keys to move to "Safe Mode with Networking" and press Enter key. Read more detailed instructions here: http://www.computerhope.com/issues/chsafe.htm
NOTE: Login as the same user you were previously logged in with in the normal Windows mode.
2. Download free anti-malware software from the list below and run a full system scan.
NOTE: in some cases the rogue program may block anti-malware software. Before saving the selected program onto your computer, you may have to rename the installer to iexplore.exe or winlogon.exe With all of these tools, if running Windows 7 or Vista they MUST be run as administrator. Launch the program and follow the prompts. Don't forget to update the installed program before scanning.
3. New threats appear every day. In order to protect your PC from such (new) infections we strongly recommend you to use ESET Smart Security.
Win Defrag associated files and registry values:
Files:
- %Temp%\[SET OF RANDOM CHARACTERS]
- %Temp%\[SET OF RANDOM CHARACTERS].exe
- %Temp%\dfrg
- %Temp%\dfrgr
- %Temp%\[SET OF RANDOM CHARACTERS].dll
- %UserProfile%\Desktop\Win Defrag.lnk
- %UserProfile%\Start Menu\Programs\Win Defrag\
- %UserProfile%\Start Menu\Programs\Win Defrag\Win Defrag.lnk
- %UserProfile%\Start Menu\Programs\Win Defrag\Uninstall Win Defrag.lnk
C:\Documents and Settings\[UserName]\Local Settings\Temp (in Windows 2000/XP)
C:\Users\[UserName]\AppData\Local\Temp (in Windows Vista & Windows 7)
%UserProfile% refers to:
C:\Documents and Settings\[UserName]\ (in Windows 2000/XP)
C:\Users\[UserName]\ (in Windows Vista & Windows 7)
Registry values:
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run "[SET OF RANDOM CHARACTERS]"
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run "[SET OF RANDOM CHARACTERS].exe"
No comments:
Post a Comment