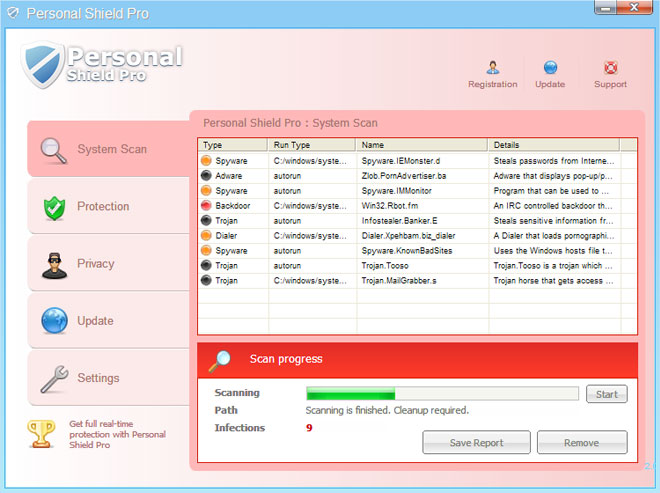
When Personal Shield Pro is running, it blocks certain application on your computer, usually Task Manager, Registry editor, other system utilities and of course legitimate anti-malware software. It displays fake notification saying that the program is infected:
Application taskmgr.exe cannot be activated. Reason: suspected in virus activitiy and moved to quarantine. Please, activate your antivirus software to clean application.Personal Shield Pro displays other fake security alerts like every on or two minutes. Thankfully, this fake AV can be removed rather easily. If you are good with computers, you can remove this fake security program manually. But if you are not that good with computers then I suggest using free anti-malware tools listed below.
Personal Shield Pro video (old graphical user interface):
OPTIONAL: In case you can't boot your PC in Safe Mode with Networking or you can't delete the malicious files manually, you can use this code 8945315-6548431 to register the rogue application in order to stop the fake security alerts. Once this is done, you are free to install anti-malware software and remove the rogue anti-virus program from your computer properly. If you need help in removing Personal Shield Pro from your computer, please leave a comment below.
Last, but not least, if you have already purchased this fake security application, please contact your credit card company and dispute the charges. Please note that you may become a victim of credit card scam or even identity theft. Additional information about this malware and comments are welcome. Good luck and be safe online!
Personal Shield Pro removal instructions (in Safe Mode with Networking):
1. Reboot your computer is "Safe Mode with Networking". As the computer is booting tap the "F8 key" continuously which should bring up the "Windows Advanced Options Menu" as shown below. Use your arrow keys to move to "Safe Mode with Networking" and press Enter key. Read more detailed instructions here: http://www.computerhope.com/issues/chsafe.htm
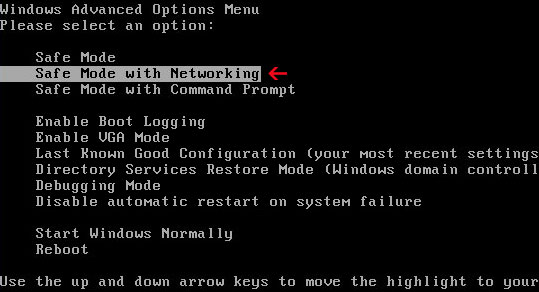
NOTE: Login as the same user you were previously logged in with in the normal Windows mode.
2. Download recommended anti-malware software (direct download) and run a full system scan to remove this virus from your computer.
3. New threats appear every day. In order to protect your PC from such (new) infections we strongly recommend you to use ESET Smart Security.
Alertane Personal Shield Pro removal instructions:
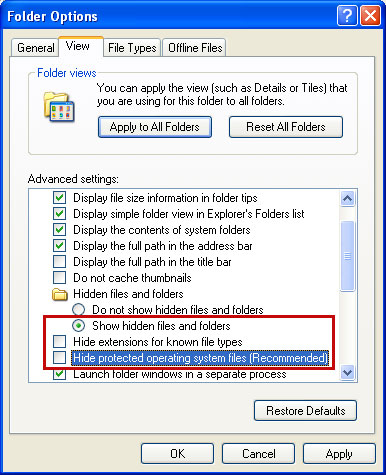
Make sure that you can see hidden and operating system protected files in Windows. For more in formation, please read Show Hidden Files and Folders in Windows.
Under the Hidden files and folders section, click Show hidden files and folders, and remove the checkmarks from the checkboxes labeled:
- Hide extensions for know file types
- Hide protected operating system files
1. Find Personal Shield Pro file(s).
On computers running Windows XP, malware hides in:
C:\Documents and Settings\All Users\Application Data\
On computers running Windows Vista/7, malware hides in:
C:\ProgramData\
2. Look for suspect ".exe" or ".pspro" files in the given directories depending on the Windows version you have.
Example Windows XP:
C:\Documents and Settings\All Users\Application Data\aYHmMJuqrr2.pspro
Example Windows Vista/7:
C:\ProgramData\aYHmMJuqrr2.pspro
Basically, there will be a malicious ".pspro" file named with a series of numbers or letters.
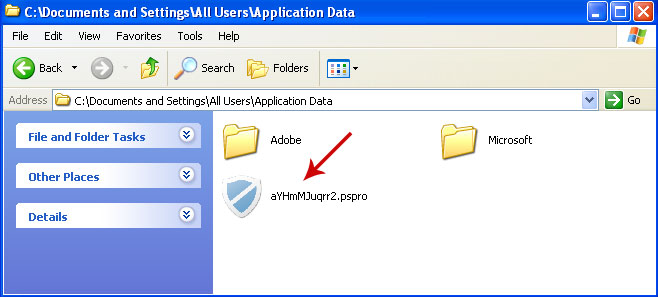
Rename aYHmMJuqrr2.pspro to aYHmMJuqrr2.vir For example:
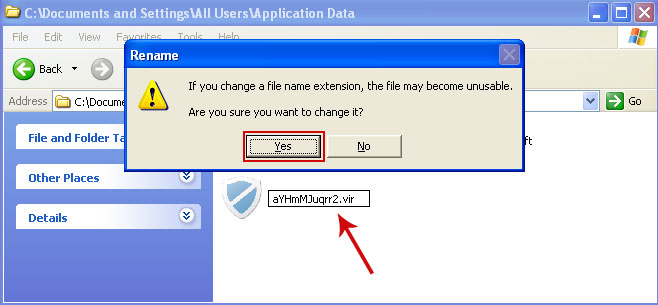
It should be: C:\Documents and Settings\All Users\Application Data\aYHmMJuqrr2.vir
Instead of: C:\Documents and Settings\All Users\Application Data\aYHmMJuqrr2.pspro
3. Restart your computer. The malware should be inactive after the restart.
4. Open Internet Explorer. Download exe_fix.reg and run it. Click "Yes" to safe the changes.
5. Download recommended anti-malware software (direct download) and run a full system scan to remove this virus from your computer.
Personal Shield Pro associated files and registry values:
Files:
Windows XP:
- C:\Documents and Settings\All Users\Application Data\[SET OF RANDOM CHARACTERS].exe
- C:\Documents and Settings\All Users\Application Data\[SET OF RANDOM CHARACTERS].pspro
- C:\ProgramData\[SET OF RANDOM CHARACTERS].exe
- C:\ProgramData\[SET OF RANDOM CHARACTERS].pspro
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run "[SET OF RANDOM CHARACTERS].exe"
- HKEY_CLASSES_ROOT\.pspro
- HKEY_CLASSES_ROOT\PSP
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run "[SET OF RANDOM CHARACTERS].pspro"
- HKEY_CLASSES_ROOT\.exe "Default" = 'PSP'
No comments:
Post a Comment