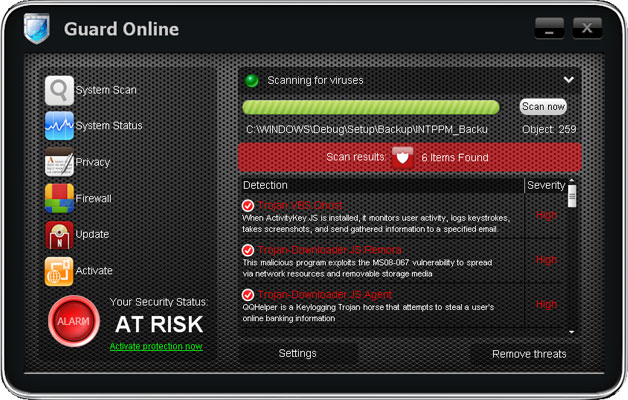
Cloud Protection is yet another rogue anti-virus product shaped like an iPhone or maybe more like an iPad just right after Jobs's death. I've just received an email from one of our readers saying just how terrible people cyber criminals can be, it's just sick, wrong. Just a few days ago they released
Guard Online malware and now there's an exact copy of this malware attempting to lure people into paying for completely useless security product. As we said before, Cloud Protection can not protect your computer from hackers, viruses, scams, and other security threats. Just because it looks nice doesn't mean anything. It can't remove viruses, spyware and other malicious software, so don't even think about purchasing it. Fake AVs continue to be more prevalent than any other type of virus trying to lure people into obtain credit card details. If your computer is infected with Cloud Protection, please follow the steps in the removal guide below.

OK, so, just like the previous version of this
scareware, Cloud Protection will actually drop a rootkit onto your computer. It's the ZeroAccess rootkit. This rootkit is being distributed very actively, thankfully, there at least a couple of tools that can handle this very sophisticated malware. You can use either
TDSSKiller or
ZeroAceess removal tool by Webroot. Both are completely free, except the the second one does't work on 64-bit systems. Anyway, to remove Cloud Protection from your computer, please follow the removal instructions below. And one more thing, if you choose to remove this virus manually, you should still run a full system scan with anti-malware tool and TDSSKiller. If you have any questions, please leave a comment below. Good luck and be safe online!
http://deletemalware.blogspot.com
Cloud Protection removal instructions:1. Download free anti-malware software from the list below and run a full system scan.
NOTE: in some cases the rogue program may block anti-malware software. Before saving the selected program onto your computer, you may have to rename the installer to
iexplore.exe or
winlogon.exe With all of these tools, if running Windows 7 or Vista they MUST be run as administrator. Launch the program and follow the prompts. Don't forget to update the installed program before scanning.
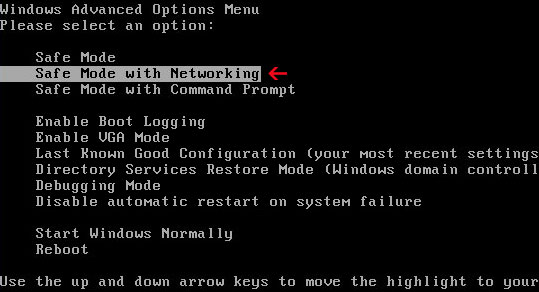
If you can't download it, please reboot your computer is "
Safe Mode with Networking". As the computer is booting tap the "
F8 key" continuously which should bring up the "
Windows Advanced Options Menu" as shown below. Use your arrow keys to move to "Safe Mode with Networking" and press Enter key. Open Internet Explorer and download STOPzilla. Once finished, go back into
Normal Mode and run it. That's It!
Read more detailed instructions here:
http://www.computerhope.com/issues/chsafe.htm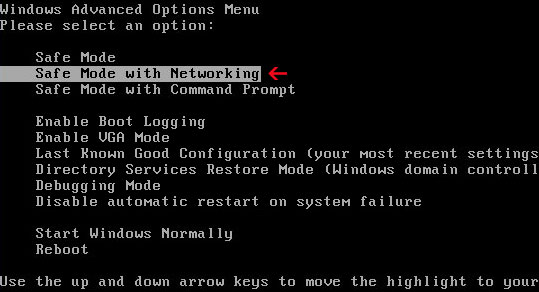
NOTE:
Login as the same user you were previously logged in with in the normal Windows mode.
2. Remove the TDSS/ZeroAccess rootkit (if exists). Please follow this removal guide:
http://deletemalware.blogspot.com/2010/03/tdss-alureon-tidserv-tdl3-removal.html
Manual Cloud Protection removal guide:1. Right-click on
Guard Online icon and select
Properties. Then select
Shortcut tab.
The location of the malware is in the
Target box.
2. In our case the malicious file was located in C:\Windows\System32 folder. Select the malicious file, rename it and change a file name extension.
Original file:
TcS22bF3nGaQWKf.exe
Renamed file:
TcS22bF3nGaQWKf.vir
3. Restart your computer. After a reboot, download free anti-malware software from the list below and run a full system scan.
4. Download free anti-malware software from the list below and run a full system scan.
NOTE: in some cases the rogue program may block anti-malware software. Before saving the selected program onto your computer, you may have to rename the installer to
iexplore.exe or
winlogon.exe With all of these tools, if running Windows 7 or Vista they MUST be run as administrator. Launch the program and follow the prompts. Don't forget to update the installed program before scanning.
5. Remove the TDSS/ZeroAccess rootkit (if exists). Please follow this removal guide:
http://deletemalware.blogspot.com/2010/03/tdss-alureon-tidserv-tdl3-removal.html
Manual activation and Cloud Protection removal:1. Choose to remove threats and manually activate the rogue program. Enter one of the following codes to activate Cloud Protection.
9992665263
1148762586
1171249582
1186796371
1196121858
1225242171
1354156739
1579859198
1789847197
1835437232
1837663686
1961232582
2. Download free anti-malware software from the list below and run a full system scan.
NOTE: in some cases the rogue program may block anti-malware software. Before saving the selected program onto your computer, you may have to rename the installer to
iexplore.exe or
winlogon.exe With all of these tools, if running Windows 7 or Vista they MUST be run as administrator. Launch the program and follow the prompts. Don't forget to update the installed program before scanning.
3. Remove the TDSS/ZeroAccess rootkit (if exists). Please follow this removal guide:
http://deletemalware.blogspot.com/2010/03/tdss-alureon-tidserv-tdl3-removal.html
Associated Cloud Protection files and registry values:Files:
- C:\WINDOWS\system32\[SET OF RANDOM CHARACTERS].exe
- C:\Documents and Settings\[UserName]\Application Data\csrss.exe
- C:\Documents and Settings\[UserName]\Application Data\hTrkd58DeORldrQCloud Protection.ico
- C:\Documents and Settings\[UserName]\Application Data\Microsoft\csrss.exe
- C:\Documents and Settings\[UserName]\Desktop\Cloud Protection.lnk
- C:\Documents and Settings\[UserName]\Local Settings\Temp\[SET OF RANDOM CHARACTERS].tmp
- C:\Documents and Settings\[UserName]\Start Menu\Programs\Cloud Protection\Cloud Protection.lnk
Registry values:
- HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run "[SET OF RANDOM CHARACTERS]"
Share this information with your friends: